With so much of your life on your iPhone, have you ever wondered how secure it really is? The Wall Street Journal reported that criminals are taking advantage of the basic iPhone unlock passcode to take over the financial accounts of innocent victims, draining bank accounts and upending their lives.
The iPhone has many convenient features that make lives easier for users, but those very same features make the iPhone easy for criminals to perpetrate theft. This blog discusses the features/vulnerabilities of the iPhone that thieves use to gain access to their victims’ financial accounts and apps, steal large sums of money, and prevent the victims from recovering access.
- An iPhone is Only as Secure as The Password That Secures It
- The iPhone passcode grants access to payment apps and passwords
- The unlock code grants access to change FaceID
An iPhone is Only as Secure as Your Password
An iPhone passcode or FaceID is the security measure standing in the way of anyone holding your iPhone and its contents. The iPhone passcode can override the need for FaceID. With the correct passcode, the iPhone unlocks and gives users access to everything, including personal data, Apple Pay, passwords, photos, videos, contacts, and messages.
The iPhone Passcode Grants Access to Apple Keychain, the Gateway to Many Accounts
In addition, the iPhone passcode gives access to Apple’s iCloud Keychain, a password management system built into Apple’s macOS and iOS operating systems. It allows users to securely store and manage passwords, credit card information, and other sensitive data. Apple Keychain is a great way to store complex passwords and maintain proper password hygiene. When a user enters a new password or credit card information on their Apple device, Keychain gives them the option to save the information to their keychain. This information is then encrypted and stored securely on the device. In addition to storing passwords and credit card information, Keychain can also store Wi-Fi network information, banking information, secure notes, and other types of sensitive data. This information can be synced across multiple Apple devices using iCloud Keychain, which allows users to access their stored information on all of their devices.
However, getting access to Keychain is too easy for some thieves. Only possession of the phone and passcode is required. Once someone gains access to Apple Keychain, they have all the ingredients to access bank accounts — the username and password, as well as the device where One Time Passcodes are sent. Using this feature, a thief who had gained access to a victim’s iPhone and passcode stole $10,000 from the victim’s bank account within mere minutes.
The Unlock Code Grants Access to Change FaceID
Apple Face ID is a secure and convenient way to unlock your iPhone by simply looking at it. However, if you know the passcode to the iPhone, you can change the Face ID settings. This is because the passcode is used as a fallback authentication method in case Face ID fails or is unavailable. To change the Face ID settings, go to the “Face ID & Passcode” section in the iPhone settings menu and enter your passcode. From there, you can turn off Face ID, add a new face, or reset the face data altogether.
How Thieves Leverage Passwords for Crime
According to the WSJ article, thieves gain physical possession of the iPhones and, through shoulder surfing (when someone peers over someone else’s shoulder to catch a glimpse of their password) and other social engineering means, they’re able to figure out the owner’s password.
- Once access to the phone is gained, the thief has free rein over all stored passwords and access to apps, and can also change the victim’s Apple ID password.
- From there, the thief can disable “Find My iPhone,” allowing them to resell the phone and prevent the victim from locating or erasing their data remotely.
How Can Financial Institutions Protect Their Customers?
A solution to this problem is to protect customers by increasing the number of authentication methods used to secure bank and financial accounts.
Currently, if a thief gains physical access to a smartphone, they also gain access to passwords, one-time passcodes, and authentication apps found on the phone. These include text messages sent to the phone and one-time passcode authentication apps commonly used for two-factor authentication.
The key is to increase authentication factors by adding a third factor that is independent of the device itself. That is where a biometric multifactor authentication comes in.
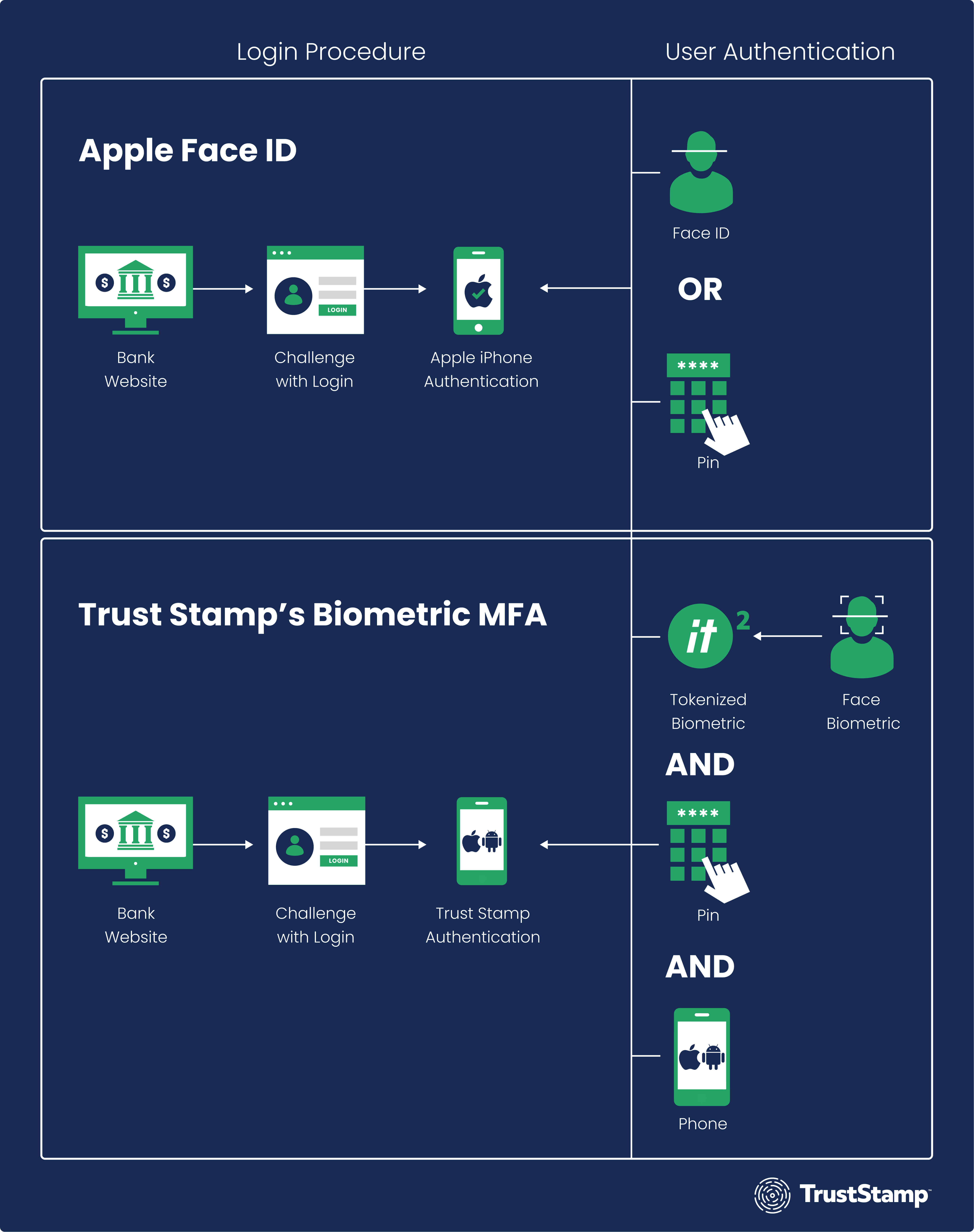
Trust Stamp’s Biometric MFA adds a low-friction and third authentication factor of a facial biometric. The Trust Stamp’s Biometric MFA solution creates a token based on a user’s facial biometric, which replaces or supplements passcodes. Biometric MFA ensures the user is the right person and is a live person. This differs from Apple’s Face ID, which actually reverts to a knowledge factor passcode.
Contact Trust Stamp today to learn how Biometric MFA improves user identification and authentication and prevents fraud for data security and user privacy.

